TURN THREAT DATA INTO DECISIVE ACTION
Extracts, structures, and connects global OSINT and darknet signals into intelligence so analysts act faster, with 50-70% less research time.
Trusted by Security Professionals
“What used to take hours of manual research now takes minutes. threatlandscape.io has fundamentally changed how we prioritize vulnerabilities. I can quickly see which CVEs are being actively exploited by the threat actors we care about.”
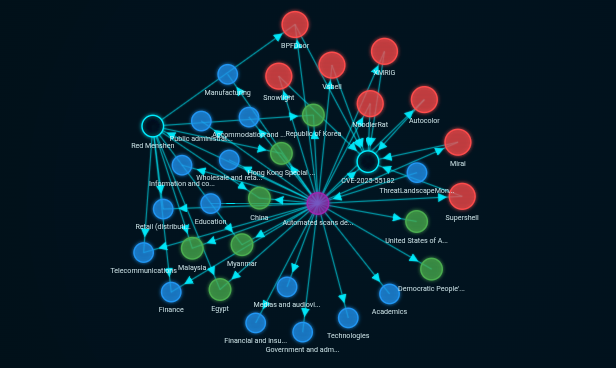
“The STIX-native structure is a game-changer. Instead of reading a 2,000-word article about a new threat actor and manually extracting IOCs, I get pre-correlated objects all linked together in a graph I can actually navigate at 2 AM when my brain is fried.”
“After several years with Feedly, we transitioned to Threat Landscape Platform — straightforward onboarding, clean interface, and actionable intelligence. A dependable addition to our security stack. I would recommend it to other SOC teams.”
Why We're Different: A Smarter Way to Threat Intelligence
While others focus on heavy workflows and rigid deployments, we focus on saving you time and enabling smarter, contextual decisions.
Legacy tools & platforms
- Manual triage across noisy feeds
- Per-seat licensing, long contracts
- Raw IOC dumps with no context
- English sources only
- Heavy manual correlation
- Hours of analyst time per report
You Get with Threat Landscape
- High-confidence intelligence, pre-filtered
- Flexible monthly pricing, no lock-in
- MITRE ATT&CK mapped + campaign-correlated
- Multilingual ingestion & analysis
- Automated cross-source trends & actor links
- 50-70% less research time
- Conversational access to threat intelligence
From overwhelming noise to actionable intelligence.
Traditional Platforms
Overwhelming noise, no context, manual filtering required
Platform
Clean insights, actionable intelligence
“The noise reduction is real. I've cut my morning threat briefings from 90 minutes of skimming RSS feeds to about 20 minutes of reviewing their curated dashboard.
Our Products
Three powerful products to meet your threat intelligence needs.
Threat Landscape Copilot
For analysts who need answers, not raw data. Ask questions in plain language and get structured, role-aware threat intelligence — grounded in live STIX 2.1 data, not static training sets.
- Conversational interface over continuously updated threat intel
- Role-aware responses tuned for CISO, Detection, IR & CTI workflows
- Surfaces actors, TTPs, IOCs & campaigns relevant to your question
- No hallucinations on threat data — every answer backed by STIX objects
- Available standalone or included free in all Platform plans
Threat Landscape Platform
For CTI, SOC, IR, and CISO teams who need structured, actionable threat intelligence — not just news feeds. Continuously updated STIX 2.1 intelligence with full provenance, darknet exposure visibility, and the context your team actually needs to act.
- Interactive dashboards & visualized threat graphs
- Curated Daily & weekly intelligence digests
- Darknet monitoring: leak-site claims, ransomware victims & criminal chatter
- Advanced search & filtering across actors, victims, vulnerabilities, countries & sectors
- MITRE ATT&CK mappings ready to be exported to MITRE Navigator
- Export to STIX & PDF — native integrations with Splunk, Sentinel, XSOAR, MISP, OpenCTI & more
Threat Intelligence APIs
Two purpose-built APIs for engineering teams — one delivering full STIX 2.1 intelligence bundles, one purpose-built for high-speed IOC ingestion. Both available over REST and TAXII 2.1.
- Intelligence API — STIX 2.1 bundles with threat actors, CVEs, TTPs & more
- IOC API — deduplicated indicators with active-window feeds per type
- REST & TAXII 2.1 — works with any compliant TIP, SIEM, or client
- Built for automation: SIEM enrichment, SOAR playbooks & custom pipelines
- Consistent schema, full provenance
- Filter by actor, sector, country, malware, CVE and more
- OpenCTI Connector available
Reduce Costs. Save Time. Scale Smarter.
Start with flexible monthly plans—scale up or cancel anytime. No long-term commitments. No Vendor Lock-In. No hidden fees.
Have questions before getting started Talk to our team